Application Protection
Genuine technology
KyberSecurity protects applications designed to operate on cloud, servers or IoT. Security engines are embedded directly into your application in automated fashion. There is no need to adapt the code source and the protection process requires no prior security knowledge. Once the security engines is inserted into the application, the protection goes wherever the application is deployed. Applications secured by KyberSecurity are self-defendable, the protection does not rely on external libraries, networking module or hardware.
|
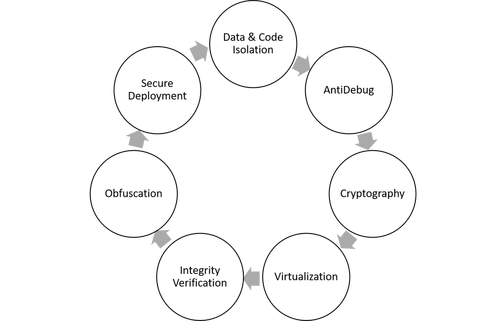
KyberSecurity protection is a suite of advanced multilayered cybersecurity technologies. Our security engines operate interconnected leveraging an outstanding protection against the most sophisticated attacks.
Security engines
|
Benefits
- Excellent security value (audited by independent security experts)
- Protected application is resilient to sophisticated and persistent attacks
- Application is always protected – no networking component, so protection is enabled even offline
- External and internal protectors enabled in a multi-layer protection approach
- Embeds security controls directly into applications enabling protection wherever the application is deployed
- Requires no changes to source code minimizing the user interaction
- Automates insertion of security engines into applications — simplifying the process
- Broadly applicable: servers, IoT, cloud and desktops
- Involves randomization on variable security specs — eliminating the risk of having one successful hack being applied to other applications
- Adapts the protection strength per application, giving greater control over the protections you desire